Helix ALM clients exchange data with the Helix ALM Server, which also exchanges data with the license server and any other Helix ALM applications you use. To keep your data secure,
To
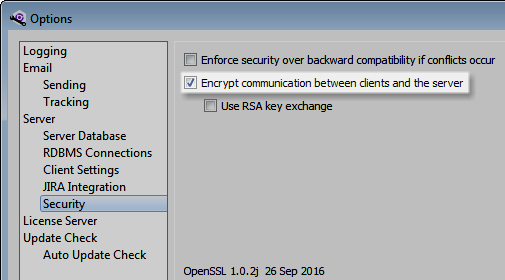
Note: The OpenSSL version used by Helix ALM is displayed with the
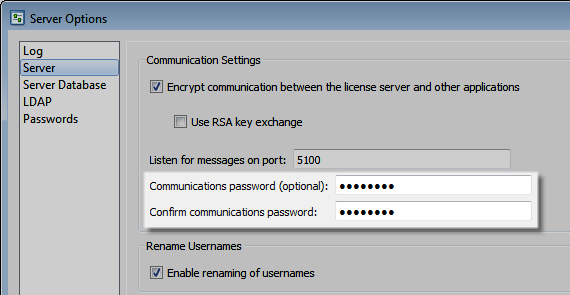
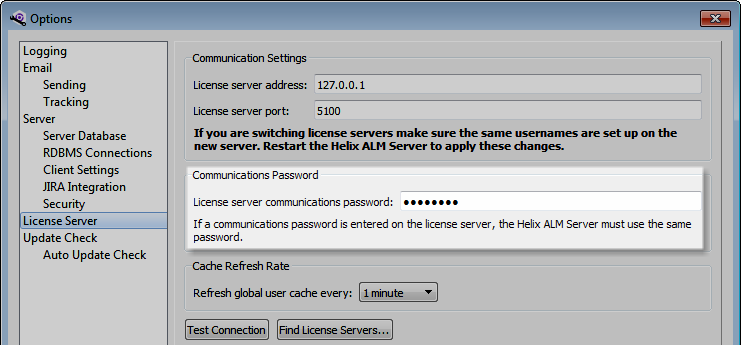
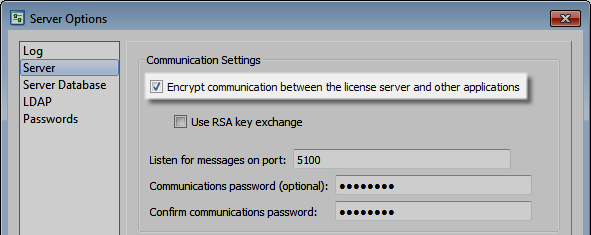
To encrypt license server communication, select Encrypt communication between the license server and other applications in the server options in the Helix ALM License Server Admin Utility.
Note: These options do not affect login credentials sent from Helix ALM web clients to the Helix ALM Server and license server. To encrypt communication between browsers and the CGI, configure HTTPS on your web server.
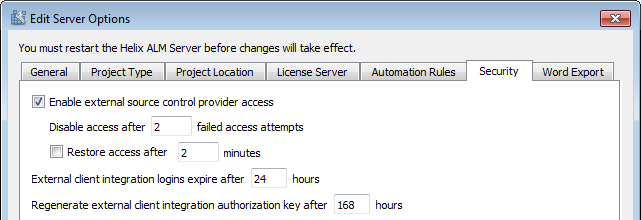
You can also use RSA key exchange on the Helix ALM Server and license server if your network is potentially insecure or any users access client applications outside your network using a username and password. RSA is a public encryption algorithm that uses separate keys for encryption and decryption, which helps prevent man-in-the-middle attacks where a hacker intercepts or alters communication between clients and servers. See Securing communication between clients and servers for information.
To
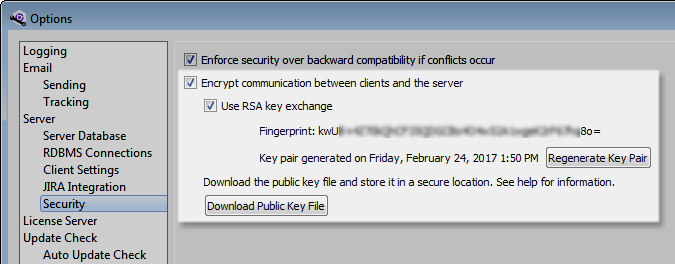
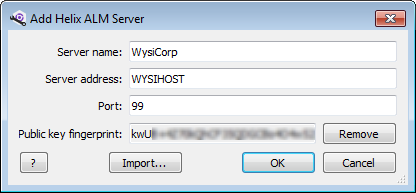
When RSA key exchange is enabled, public and private key files are generated and clients can only connect to the server when the correct key is exchanged. The key files remain on the server hard drive. Download the server settings XML file to a secure location and distribute it to authorized users so they can import the public key fingerprint in client applications used to connect to the
Tip: Update security permissions on the RSA key files to better protect them. Only the server needs read and modify access to the private and public key files on the server computer. All users need read access to the downloaded server settings file, but only administrative users should have access to modify it. See the operating system help for information about file security.